MEV Learning Module
Before transactions ever make it on-chain, they pass through a hidden battleground. Validators, traders, and bot operators compete fiercely to reorder transactions in their favor, profiting handsomely in the process.
We call this MEV (Maximal Extractable Value)—the pursuit of maximum profit during block production. While the average user may not notice it, within the industry, MEV is often described as an “invisible tax,” underscoring its growing impact on the blockchain economy.
In this article, we’ll explore the fundamentals of MEV and the challenges it poses. We’ll also introduce a MEV Learning Module, which provides a sandboxed EVM environment for hands-on experience in implementing MEV strategies. Let’s dive in.
How MEV Works
To understand MEV, we first need to look at how transactions are processed on a blockchain. We’ll use Ethereum (EVM) as our example, noting that not all blockchains follow the same exact structure.
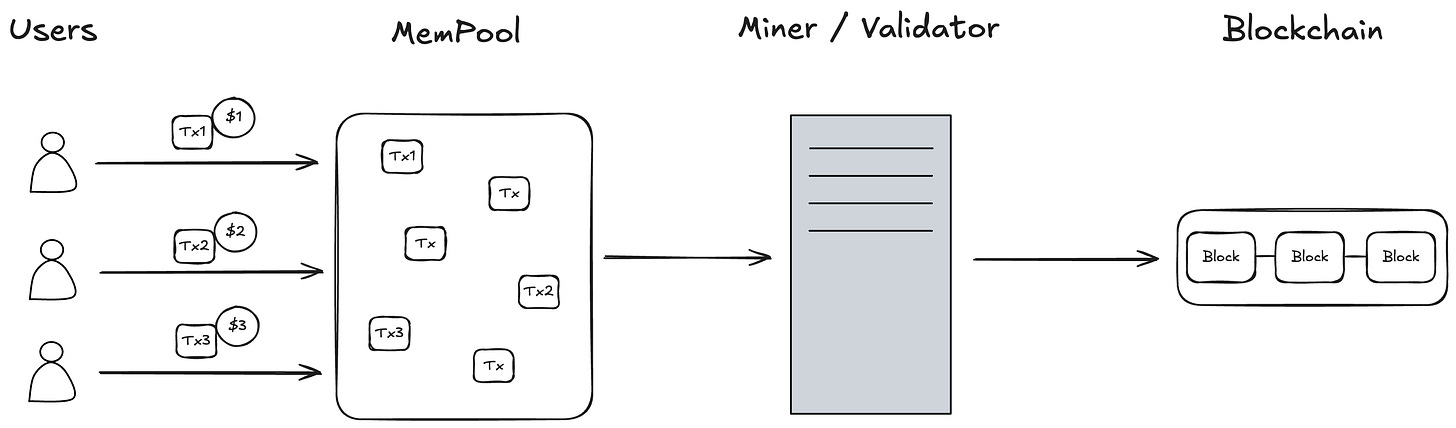
User
Most users generate and sign transactions—such as sending ETH or swapping tokens—through wallets like MetaMask.Mempool
Once created, a transaction doesn’t go straight into a block. Instead, it’s placed in a public Mempool (a waiting area) shared by blockchain nodes:The Mempool holds transactions not yet included in a block.
Because the Mempool is public, anyone can see these pending transactions.
Miner/Validator
In Proof-of-Work, miners; in Proof-of-Stake, validators select transactions from the Mempool to build new blocks.
Generally, block producers pick transactions that pay higher gas fees first to maximize their own profit.
Blockchain
Once a transaction is included in a block, that transaction is considered confirmed.
Because the Mempool is public, it inadvertently becomes a source of MEV opportunities. Anyone who can see pending transactions has a window to reorder, front-run, or otherwise strategize to capture additional profit.
Ethereum is a Dark Forest offers a vivid real-world account of MEV. The author compares Ethereum to a dark forest, where front-running bots lurk like predators waiting to pounce on unsuspecting transactions. This analogy illustrates how transparency can paradoxically enable hidden conflicts. Being able to view pending transactions in real time creates an environment where opportunistic players can exploit that visibility.
MEV Strategies
Below are some of the most common strategies used to extract MEV.
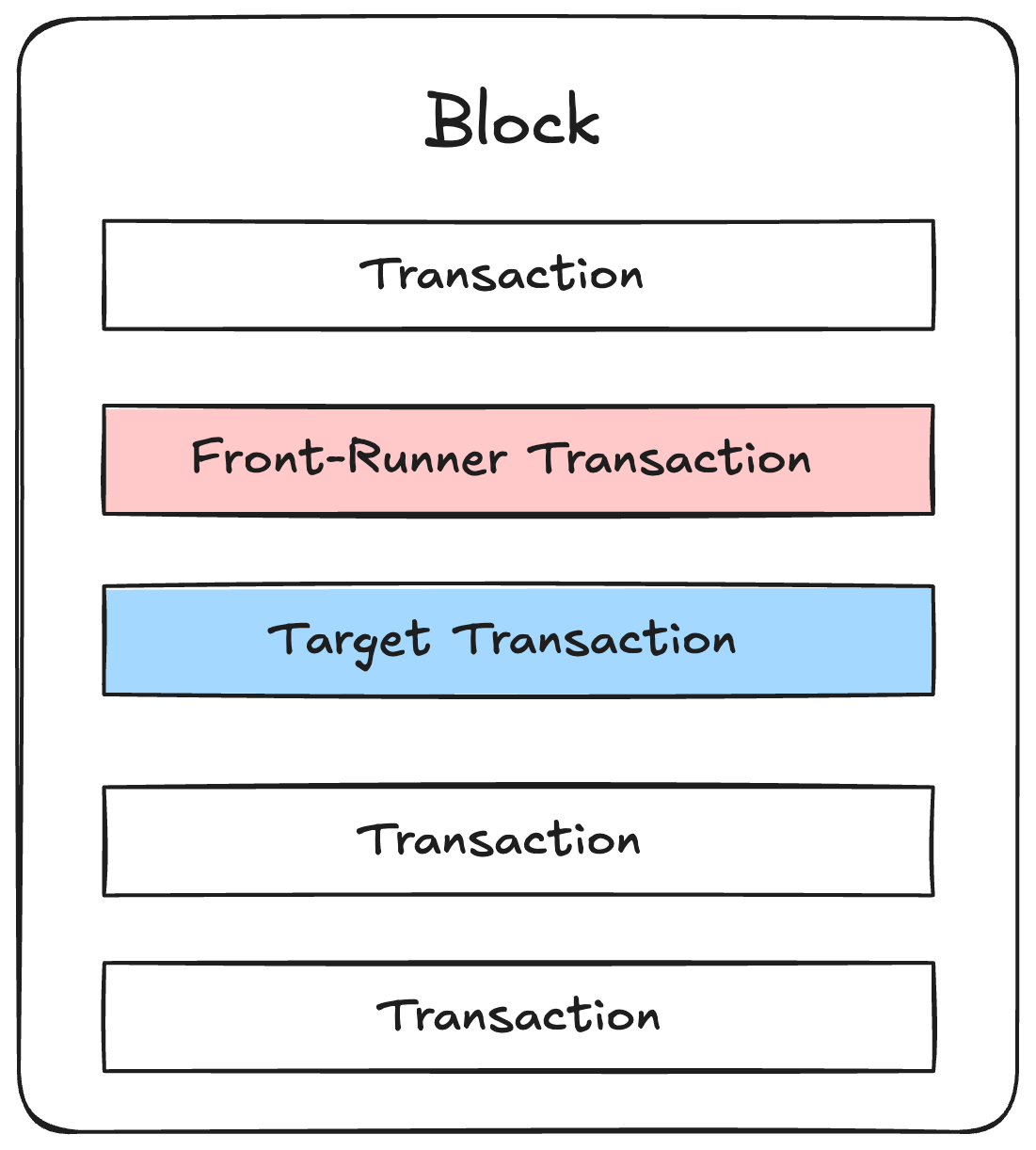
Front-Running
Front-running involves detecting someone else’s transaction in the Mempool and submitting your own transaction first so it executes ahead of theirs.
In the previously mentioned Ethereum is a Dark Forest, we can observe a real-world example of Front Running. To simplify it, let’s assume there’s a contract where a password is entered to access a vault.
contract Vault {
bytes32 private hashedPassword;
constructor(bytes32 hashedPassword) {
hashedPassword = hashedPassword;
}
function withdraw(string memory password) public {
if (keccak256(abi.encodePacked(password)) == hashedPassword) {
payable(msg.sender).transfer(address(this).balance);
}
}
}If someone who knows the password sends a transaction to withdraw funds, as soon as that transaction appears in the Mempool, an MEV bot could detect it, copy the password, and submit its own transaction first—stealing the funds before the original user’s transaction even executes.
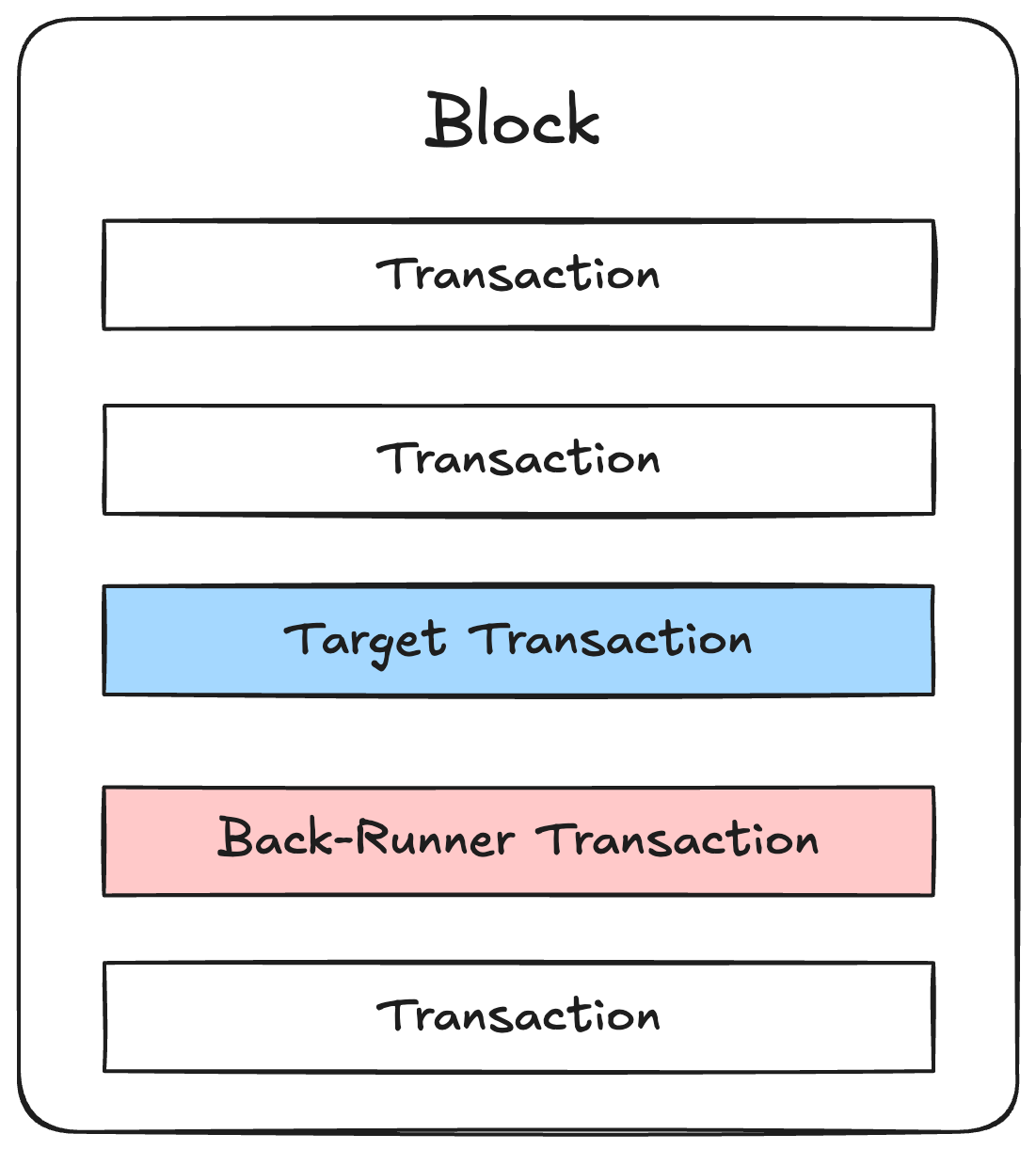
Back-Running
Back-running is the opposite of front-running: you intentionally place your transaction after another transaction.
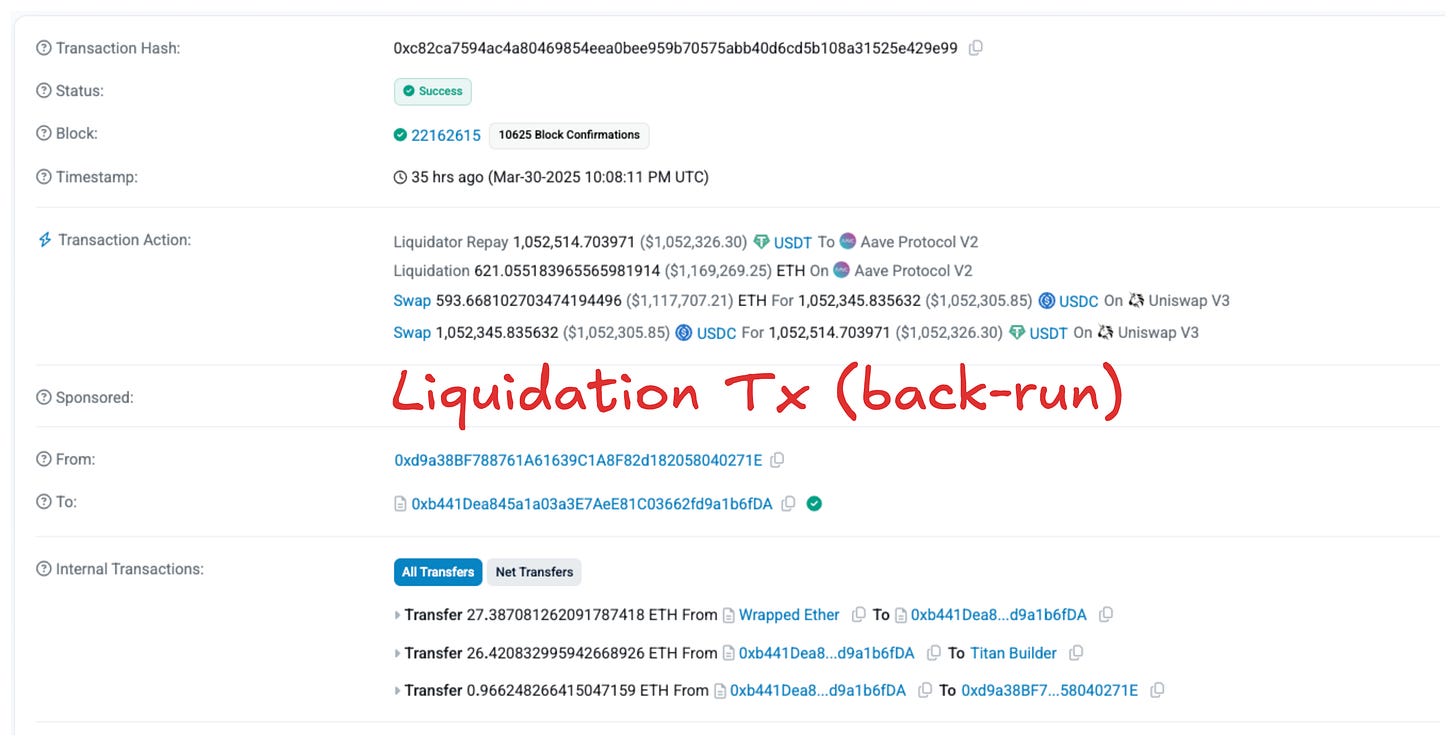
In a Lending Protocol, there is the concept of liquidation. When the value of a borrower’s collateral falls below the value of the loaned asset, a third party can repay the collateral on behalf of the borrower and acquire the loaned asset at a discount to prevent losses for the Lending Protocol. The example below shows how in AAVE2, USDT (collateral) is repaid on behalf of the borrower, and ETH is acquired at a lower price.
Liquidation occurs when the value of the assets changes. Therefore, Liquidation Transactions follow the transactions that update the Lending Protocol’s prices and trigger liquidation immediately after the update.
Sandwich Attack
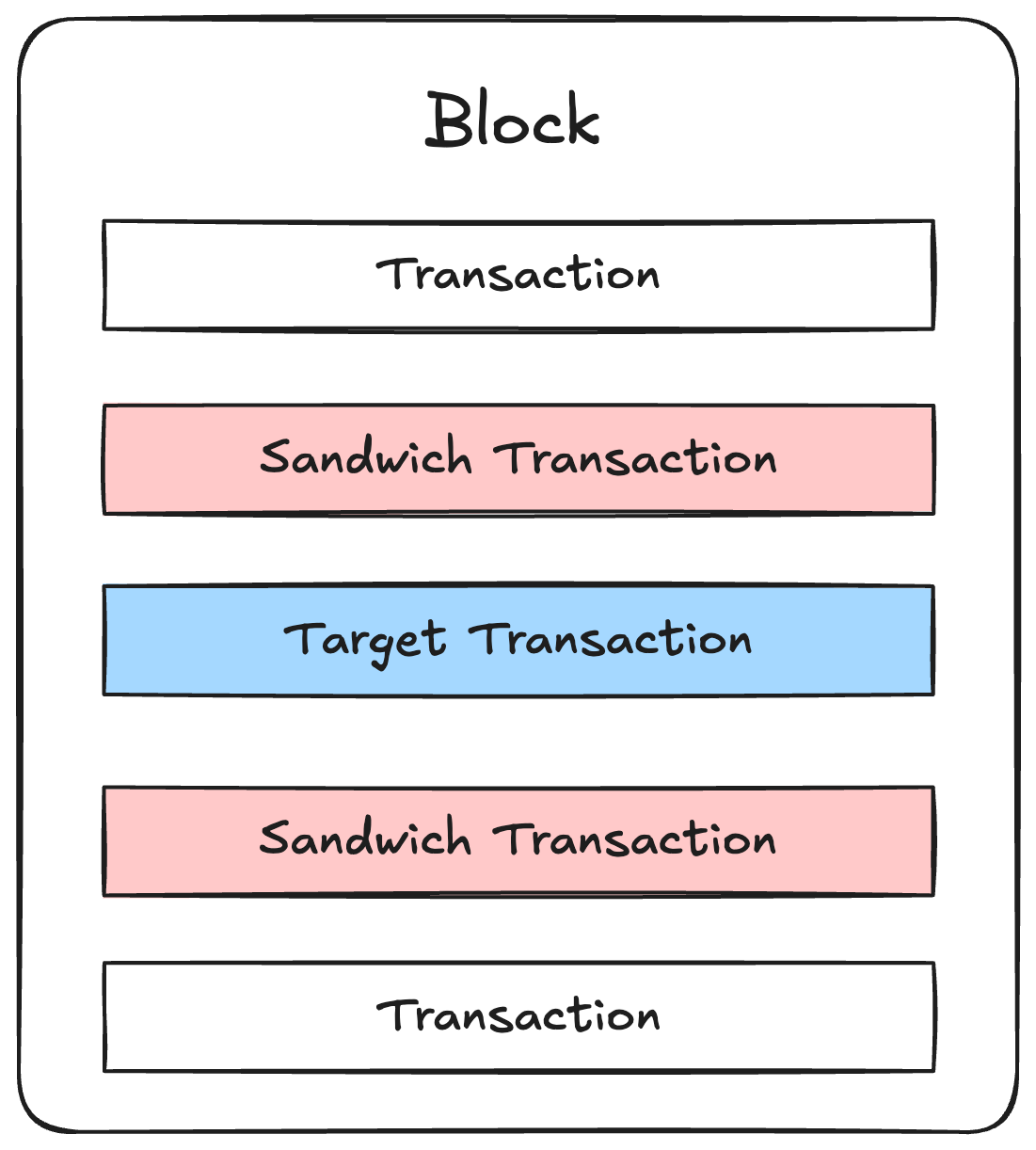
A sandwich attack combines front-running and back-running. You insert your transactions both before and after someone else’s transaction, effectively “sandwiching” it.
Detect a large swap pending in the Mempool.
Place a buy transaction first (front-run) to push the token’s price up.
Let the target user’s swap execute at this higher price.
Immediately sell (back-run) to cash in on the price difference.
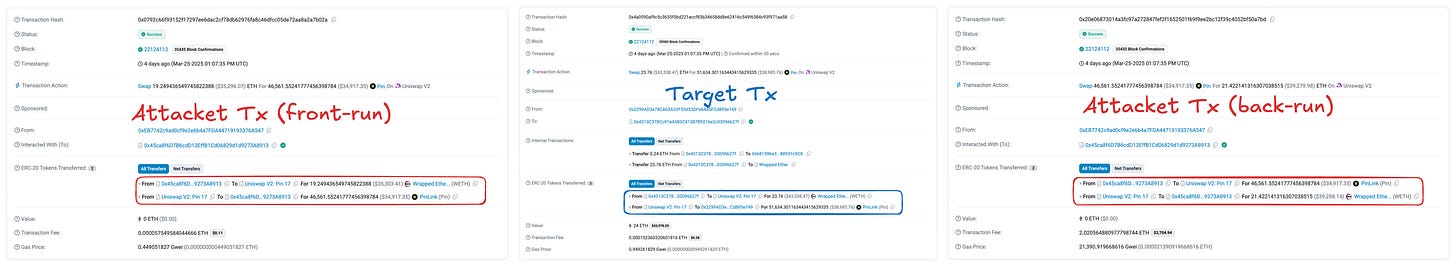
As a result, the victim’s swap faces worse slippage, while the attacker profits from this manipulation. Below is a real example on Etherscan, where the attacker’s front-run and back-run transactions flank the target user’s swap.
Below is an actual example of a sandwich attack on Etherscan:
The attacker detects a pending swap in the Mempool, then places a Front Run Tx to buy and a Back Run Tx to sell, sandwiching the user’s Target Tx in between.
And More…
MEV isn’t limited to front-running and sandwich attacks. There are many other tactics—like arbitrage, NFT minting races, and just-in-time liquidity.
Problems & Future Solutions
MEV brings several challenges:
Network trust Erosion
If a single block producer consistently monopolizes MEV, it undermines the network’s decentralization and damages user trust in the system.
User Harm
Attacks like sandwiching directly cause real losses to ordinary users, making the blockchain ecosystem less appealing.
Reduced Usability
Intense MEV competition often leads to spikes in gas fees or network congestion, diminishing overall usability.
However, some forms of MEV—like arbitrage or liquidations—can improve market efficiency. Even so, negative impacts have spurred efforts to mitigate or manage MEV.
Here are some different ways to solve MEV problems:
Application-Level Solutions
CoW Swap: Matches users who want to trade opposite sides of the same pair directly, helping to prevent sandwich attacks by eliminating the need for a public on-chain swap.
Middleware
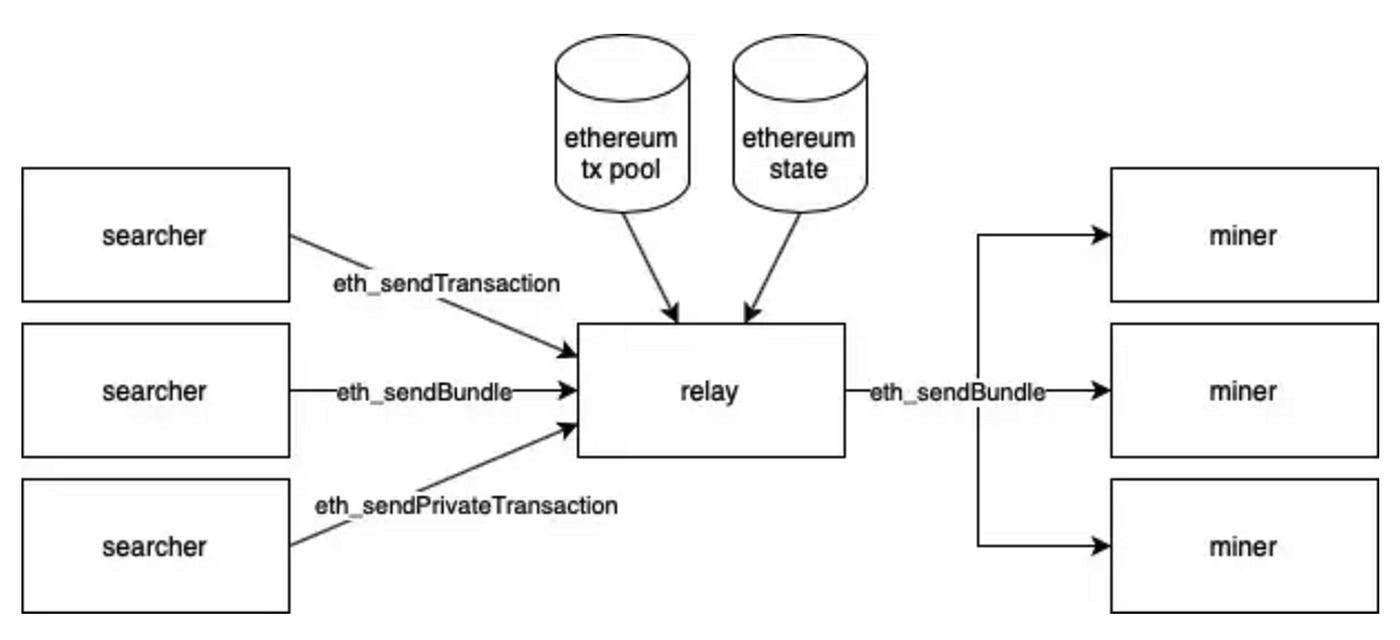
FlashBots: Bypasses the public Mempool via a private relay.
Searchers create bundles of transactions designed to extract MEV.
A Relay validates these bundles.
Miners/Validators then choose the most profitable bundle to include.
Although it requires dedicated infrastructure, FlashBots is an example of tackling MEV at the middleware level.
Protocol-Level Solutions
Proposer-Builder Separation (PBS): Splits block production into two roles—“Builders,” who extract MEV, and “Proposers,” who select which blocks to finalize. Separating responsibilities can help prevent a single entity from unilaterally reordering transactions and monopolizing MEV, thereby supporting network decentralization.
Conclusion
MEV has evolved into a pivotal aspect of blockchain economics. The inherent transparency of blockchains allows creative strategies like front-running, back-running, and sandwich attacks to thrive. However, not all MEV is detrimental; certain forms, such as arbitrage and liquidations, can enhance overall market efficiency.
As MEV grows more complex, the industry is actively pursuing solutions at multiple layers—applications, middleware, and protocols. This MEV Learning Module offers hands-on opportunities to experiment with these strategies in a sandboxed environment. By understanding how MEV works in practice, we can better develop and support safer, more efficient blockchain ecosystems for everyone.